A system typically should be designed using a "defence-in-depth" approach. That means the system architecture should reduce the likelihood, that a compromised architectural element would result in an more likely attack to another architectural elements. In order to understand the likelihood, the implications and dependencies of attacks, they can be modeled as first-class elements in medini.
Attacks are generally kept in attack collections. Those collections may represent existing knowledge about known (manifested) attacks or may define assumed (hypothetical) attacks.
Select an arbitrary package in the project and use "New | Collection | Attack Collection". Give the collection an expressive name to summarize the reasoning behind this collection. Note, that there may be numerous attack collections in the project or just one.
Open the attack list and use the "+" button to create new attacks in the collection. The name of the attack shortly describes the attack method and is used throughout the tool as the label of the attack. Give the attack a more detailed description and a suitable category. Categories are neither mandatory nor predefined, however, they are beneficial to group but also distinguish attacks (for example, separate "physical" from "communication" attacks)
The parameters for the likelihood level of an attack can be define in the collection table, for example "Expertise" and "Equipment"
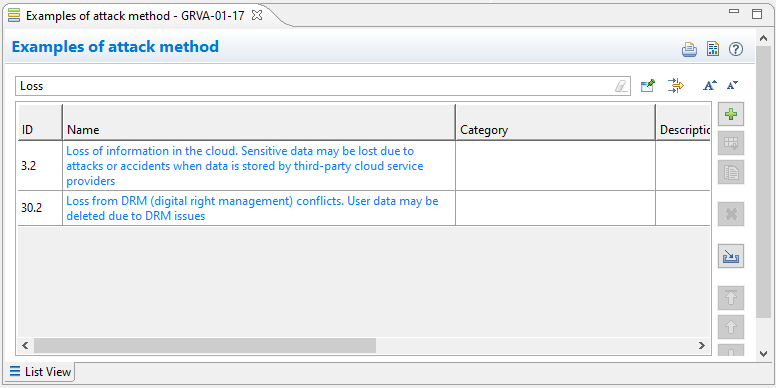
An example:
A sample collection of known attack methods is created, addressing mainly communication attacks in the internet
One attack method is generic "Loss of information in the cloud". The description says "Sensitive data may be lost due to attacks or accidents when data is stored by third-party cloud service providers". That's a typical communication attack, so category is set to "Communication"
The attack can be executed nowadays with "Standard" equipment by any "Layman". The knowledge about the TOE might be "Restricted" but the window of opportunity is "Unlimited" which in the end gives a "Critical" likelihood level.