Potential threats can be identified using various different methods and techniques. Threats can be identified for example in a simple brainstorming session or by deriving misuse cases from known use cases. To achieve the best suitable result, the method should be repeatable, easy applicable and shall achieve a high coverage of threats. The STRIDE method for example, originally implemented by Microsoft for large IT systems, is supported by the tool as an automation step and can be used to find threats to a system.
Threat identification such as STRIDE always starts from a system model. Perform the following steps once or repeat them as often as required:
Select one or more system model element, package, or model. The identification automation algorithm will drill down all selected elements to detect assets. A typical starting point would be a SysML model.
Use "Derive | Threats..." to start the threat identification automation. In the upcoming dialog select an existing Threat Collection, otherwise a new one will be always created. As a shortcut you can include any existing Threat Collection in the initial selection. That way it will automatically appear in the dialog.
The automation offers two modes which you can choose from. One is based on security attributes, the other one on the component type. While the outcome highly depends on the mapping settings configured in the project, they have in common that the algorithm will map attributes or component types to threat categories. For each category a separate threat is identified.
Identified threats will be added to the selected collection if and only if no threat with the same category exists yet for an asset. Note that no threat will be removed from the collection by the automation.
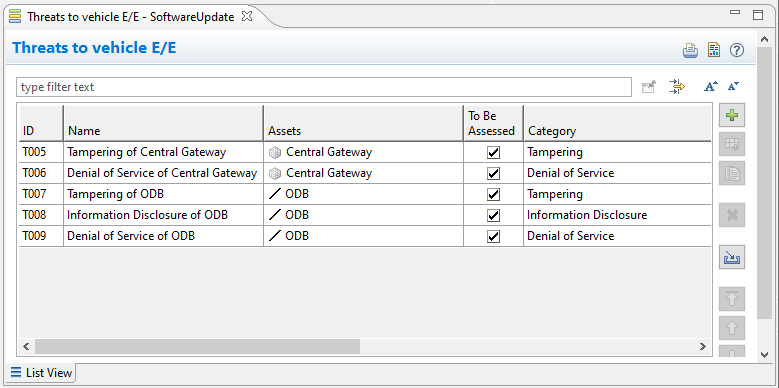
An Example:
The system architecture contains two elements connected with a single connector. The first element is marked as an asset, having two security attributes added, "Integrity" and "Availability". The second element and the connector are not marked as Assets.
The threat identification is started on the system model. Threats are identified based on the "security attributes".
The algorithm creates a new threat collection and inside two new threats, both referencing the first element (as an asset) having different threat categories depending on the mapping. In this example "Integrity" is mapped to "Tampering" and "Availability" to "Denial of Service" which is the default mapping.
The connector is marked as an asset in a second iteration and the algorithm is triggered again, this time selecting the project and the collection and using the "component type" as identification option
Three new threats are identified for the connector with a threat categories "Tampering", "Information Disclosure" and "Denial of Service" which is the default for this type. Any subsequent execution with the same settings will not create any new threat if the system model is not changed.