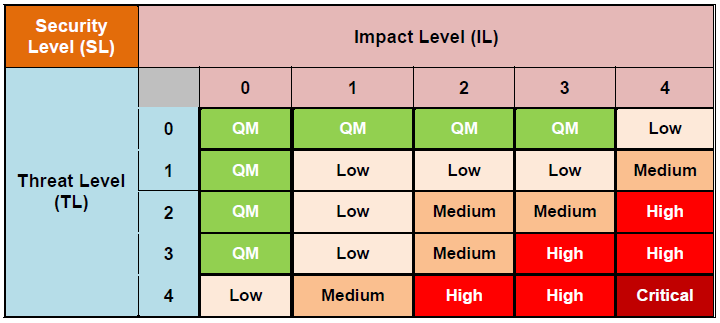
The risk assessment ultimately is about "ranking" threats, using a certain "security or risk level". The tool follows the approach that was proposed by the HEAVENS project, which is basically a three steps approach:
The Threat Level (TL) is determined, corresponding to the estimation of the "Likelihood"
The Impact Level (IL) is determined, corresponding to the estimation of the "Impact"
The final Security Level (SL) or Risk Level is determined based on TL and IL, corresponding to the final risk rating
For each of these levels, the HEAVENS project precisely defines and describes the individual parameters, their values and the final risk graph including numeric values and weights. The following three chapters are completely taken from the HEAVENS project documentation and therefore quoted.
Note: the following information was taken from the HEAVENS project documentation. Each of the parameters is backed by a numeric value that was added for completeness.
"The parameter ‘Expertise’ refers to the level of generic knowledge of the underlying principles, product type or attack methods that are required to carry out an attack on the TOE. The identified levels are as follows"
"‘Layman’ is unknowledgeable compared to experts or proficient persons, with no particular expertise; Examples may include persons who can only follow simple instructions that come with the available tools to mount simple attacks, but not capable of making progresses himself/herself if the instructions or the tools do not work as expected." (Value 0)
"‘Proficient’ persons have general knowledge about the security field and are involved in the business, for example, workshop professionals. Proficient persons know about simple and popular attacks. They are capable of mounting attacks, for example, odometer tuning and installing counterfeit parts, by using available tools and if required, are capable of improvising to achieve the desired results." (Value 1)
"‘Experts’ are familiar with the underlying algorithms, protocols, hardware, structures, security behavior, principles and concepts of security employed, techniques and tools for the definition of new attacks, cryptography, classical attacks for the product type, attack methods, etc. implemented in the product or system type." (Value 2)
"The level ‘Multiple Experts’ is introduced to allow for a situation, where different fields of expertise are required at an Expert level for distinct steps of an attack." (Value 3)
"The parameter ‘Knowledge about TOE’ refers to the availability of information about the TOE and the community size that possesses knowledge about the TOE from an attacker perspective. This parameter points to the sources from where attackers can gain knowledge about the TOE and indicates how easy or difficult it can be for an attacker to acquire knowledge about the TOE. Identified levels are as follows:"
"‘Public’ information concerning the TOE (e.g. as gained from the Internet, bookstore, information shared without non-disclosure agreements);" (Value 0)
"‘Restricted’ information concerning the TOE (e.g. knowledge that is controlled within the developer organization and shared with other organizations, for example, between suppliers and OEMs, under a non-disclosure agreement). Examples include requirements and design specifications, internal documentation." (Value 1)
"‘Sensitive’ information about the TOE (e.g. knowledge that is shared between discrete teams within the developer organization, access to which is constrained only to members of the specified teams). Examples include restricted ECU configuration parameters to enable/disable features in vehicles, vehicle configuration database, software source code." (Value 2)
"‘Critical’ information about the TOE (e.g. knowledge that is known by only a few individuals, access to which is very tightly controlled on a strict need to know basis and individual undertaking). Examples include secret root signing key." (Value 3)
"The parameter ‘Equipment’ refers to the equipment required to identify or exploit vulnerability and/or mount an attack."
"‘Standard’ equipment is readily available to the attacker, either for the identification of vulnerability or for an attack. This equipment may be a part of the TOE itself (e.g. a debugger in an operating system), or can be readily obtained (e.g. Internet downloads, protocol analyzer or simple attack scripts). Examples include simple OBD diagnostics devices, common IT device such as notebook." (Value 0)
"‘Specialized’ equipment is not readily available to the attacker, but could be acquired without undue effort. This could include purchase of moderate amounts of equipment (e.g. power analysis tools, use of hundreds of PCs linked across the Internet would fall into this category), or development of more extensive attack scripts or programs. Examples include in-vehicle communication devices (e.g., CAN cards), costly workshop diagnosis devices. If clearly different test benches consisting of specialized equipment are required for distinct steps of an attack this would be rated as bespoke." (Value 1)
"‘Bespoke’ equipment is not readily available to the public as it may need to be specially produced (e.g. very sophisticated software), or because the equipment is so specialized that its distribution is controlled, possibly even restricted. Alternatively, the equipment may be very expensive." (Value 2)
"The level ‘Multiple Bespoke’ is introduced to allow for a situation, where different types of bespoke equipment are required for distinct steps of an attack." (Value 3)
"The parameter ‘Window of opportunity’ combines access type (e.g., logical, physical) and access duration (e.g., unlimited, limited) that are required to mount an attack on the TOE by an attacker. The different levels include:"
"‘Unlimited’: High availability via public/untrusted network without any time limitation (i.e., TOE/asset is always accessible). Logical or remote access without physical presence and time limitation as well as unlimited physical access to the TOE/asset. Examples include wireless or via Internet (e.g., V2X or cellular interfaces)." (Value 0)
"‘Large’: High availability and limited time. Logical or remote access without physical presence." (Value 1)
"‘Medium’: Low availability of the TOE. Limited physical and/or logical access to the TOE. Physical access to vehicle interior or exterior without using any special tool (e.g., opening the hood to access wires)." (Value2)
"‘Small’: Very low availability of the TOE. Physical access required to perform complex disassembly of vehicle parts to access internals to mount an attack on the TOE." (Value 3)
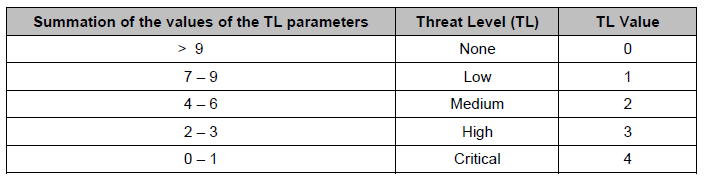
The values for each parameter are added. The sum finally defines "ranges to determine a threat level". HEAVENS defines five different threat levels (None, Low, Medium, High, and Critical). The mapping is shown in the following picture:
Note: the following information was taken from the HEAVENS project documentation. Each of the parameters is backed by a numeric value that was added for completeness.
"The ‘Safety’ parameter to estimate the safety impact is adopted from the ISO 26262"
"None" = "No injury" (Value 0)
"Low" = "Light and moderate injuries" (Value 10)
"Medium" = "Severe and life-threatening injuries (survival probable)" (Value 100)
"High" = "Life-threatening injuries (survival uncertain), fatal injuries" (Value 1000)
"The ‘Financial’ category considers all financial losses or damages that can be either direct or indirect. Direct financial damages may include product liability issues (e.g., penalties, recalls), legislation issues (e.g., penalties due to nonconformance), product features (e.g., loss in business due to illicit activation of sellable features). [...] Also, safety issues may contribute to financial damages. For example, recent recalls of certain models of cars by several OEMs due to various safety issues have financial impact on each of the OEMs. To summarize, the financial damage is the sum of direct and indirect costs for the OEM and the root cause may originate from any of the stakeholders."
"None" = "No discernible effect. No appreciable consequences" (Value 0)
"Low" = "The financial damage remains tolerable to the organization" (Value 10)
"Medium" = "The resulting damage leads to substantial financial losses, but does not threaten the existence of the organization" (Value 100)
"High" = "The financial damage threatens the existence of the organization" (Value 1000)
"The ‘Operational’ category includes operational damages caused by unwanted and unexpected incidents. Examples of such operational damages include loss of secondary (e.g., cruise control) and comfort/entertainment (e.g., cd-player, air-conditioning) functionalities of the vehicle. However, in certain situations, operational damages may cause safety and financial damages. For example, operational damages in the form of loss of primary and safety-related vehicle functionalities may affect safety of passengers and road users. Consequently, the impact of the operational category on the overall impact is relatively lower with respect to the safety and financial categories. [...] We adapt the vehicular defect severity categorization such as FMEA (Failure Mode and Effects Analysis) to classify the operational damages."
"None" = "No effect" (Severity 1, Value 0)
"Low" = "Minor to Moderate disruption" (Severity 2-3, Value 1)
"Medium" = "Moderate to Significant disruption" (Severity 5-7, Value = 10)
"High" = "Major disruption to Fails to meet safety or regulatory requirements" (Severity 8-10, Value 100)
"The ‘Privacy and legislation’ category includes damages caused by privacy violation of stakeholders (e.g., fleet owner, vehicle owner, driver) and/or violation of legislations/regulations (e.g., environmental, driving). We merge privacy and legislation into one parameter because privacy may be enforced through legislation and there exist legislations that are not related to privacy. Usually, such damages do not have direct injury, financial and operational dimensions. However, in certain situations, privacy and legislation violations may cause financial (e.g., fine, loss of access to certain market) and operational damages to the stakeholders. Consequently, the impact of the privacy and legislation category is relatively lower with respect to the safety and financial categories."
"None" = "No discernible effects in relation to violations of privacy and legislation" (Value 0)
"Low" = "Privacy violations of a particular stakeholder (e.g., vehicle owner, driver) which may not lead to abuses (e.g., impersonation of a victim to perform actions with stolen identities)" (Value 1)
"Medium" = "Privacy violations of a particular stakeholder (e.g., vehicle owner, driver) leading to abuses (e.g., impersonation of a victim to perform actions with stolen identities) and media coverage" (Value 10)
"High" = "Privacy violation of multiple stakeholders (e.g., fleet owners, multiple vehicle owners and multiple drivers) leading to abuses (e.g., impersonation of a victim to perform actions with stolen identities). Such a level of privacy violation may lead to extensive media coverage as well as severe consequences in terms of loss of market share, business operations, trust, reputation and finance for OEMs and fleet owners" (Value 100)
"In the HEAVENS model, we assign different weights to the different impact parameters. The ‘Safety’ and ‘Financial’ parameters have equal weights while estimating the overall impact level. The impact of safety and financial parameters can lead to the most severe consequences for stakeholders, for example, vehicle occupants may not survive, organizations may bankrupt. On the other hand, the impact of ‘Operational’ as well as ‘Privacy and legislation’ parameters on the overall impact is relatively lower with respect to the safety and financial damages. To reflect this fact during impact level estimation, we reduce the corresponding factors by a magnitude of one in case of operational as well privacy and legislation with respect to the safety and financial parameters."
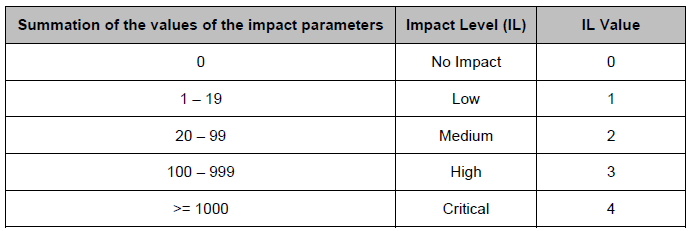
The values for each parameter are added. The sum finally defines ranges to determine a impact level. HEAVENS defines five different impact levels (None, Low, Medium, High, and Critical). The mapping is shown in the following picture:
Note: the following information was taken from the HEAVENS project documentation.
"In the HEAVENS security model, we combine Threat Level (TL) and Impact Level (IL) to derive Security Level as shown in Table [...]. The security level is set to ‘Critical’ if and only if both TL and IL have the value 4 (‘Critical’)."