| Safety and Security Support | With 2020 R1, ANSYS medini analyze supports the systematic, model-based Cybersecurity Threat Identification and Analysis. The release comes with a brand-new Cybersecurity tier, including a dedicated perspective, new project templates to start with, new modeling concepts and support for new analysis methods such as Asset Identification, Threat Analysis and Risk Assessment (TARA) and Attack Tree modeling. The feature set is compliant with Cybersecurity standards, like the upcoming ISO 21434 and related security standards. Like the safety tier, the cybersecurity analysis part offers system-oriented Cybersecurity Analysis with single-source principle for security properties based on SysML. Safety and Cybersecurity are offered in "one tool", ensuring both system safety and at the same time safeguarding the system from increasingly sophisticated attacks. |
| Asset Identification | Any system model element in a system architecture can be marked as Asset, including the definition of its security attributes. The set of potential security attributes, like the well-known CIA triad "Confidentiality", "Integrity" and "Availability" can be customized in the project settings, for example to CIAAA or HEAVENS (HEAling Vulnerability to ENhance Software Security). 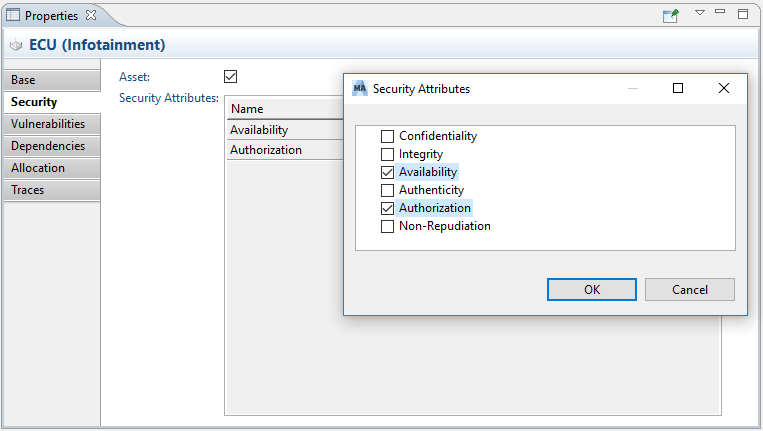 |
| Stakeholder modeling | Stakeholders can be individually modeled including their relationships and interest in Assets. Each stakeholder may have certain objectives and acceptance criteria as for example defined in HEAVENS. These settings can be customized in the project settings. 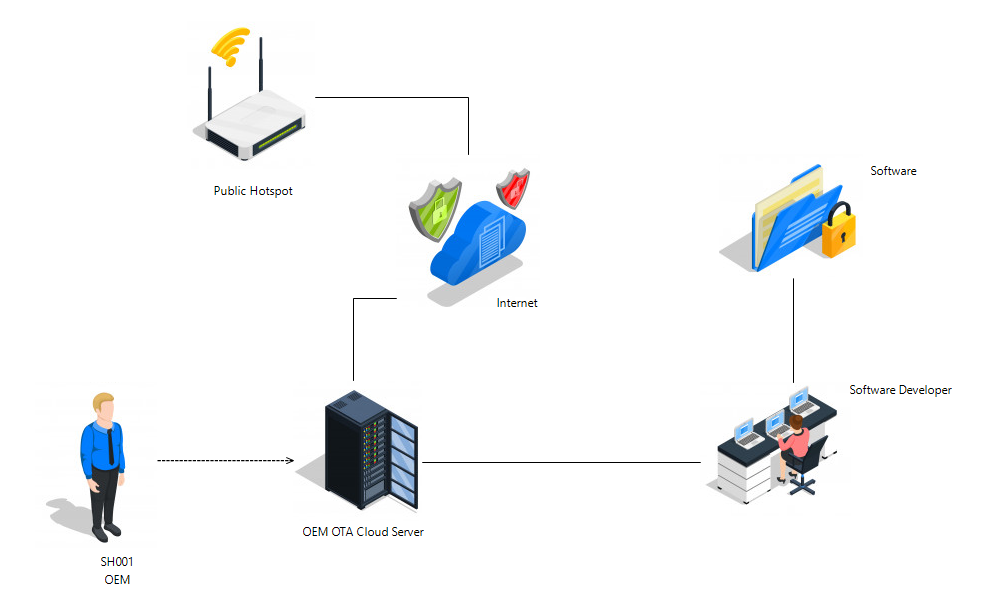 |
| Threats, Vulnerabilities, and Attack Modeling | New base concepts for cybersecurity modeling are introduced with 2020 R1, namely Vulnerabilities, Attacks and Threats. They can be either annotated at SysML elements or maintained in collections. Known manifested or new hypothetical attacks, for example, can be maintained in Attack Collections. The likelihood level of every single attack can be pre-estimated in those collections. 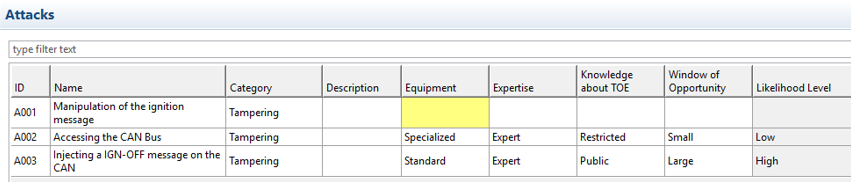 |
| Threat Identification | A systematic and iterative threat identification based on STRIDE (Spoofing, Tampering, Repudiation, Information disclosure, Denial of service, Elevation of privileges) is supported with 2020 R1. Threats can be automatically derived for all identified assets based on their security attributes or component type. The used mappings from attributes or types to STRIDE threat categories can be easily configured and customized. 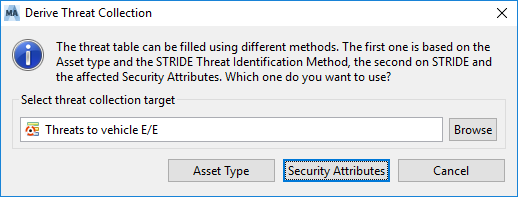 |
| Threat Analysis and Risk Assessment (TARA) | Identified Threats can be collected and maintained in Threat Collections. Their likelihood levels can be pre-estimated based on individual likelihood parameters, leading to a decision to further analyze and assess the potential risk of the threat. The Risk Assessment for threats is supported in TARA editors; pre-estimated likelihood parameters are overtaken, and the impact levels can be estimated. Out of likelihood and impact level an overall security / risk level is calculated based on the HEVANS risk graph. Based on the acceptance criteria of the corresponding stakeholders, mitigation measures can be defined and applied. 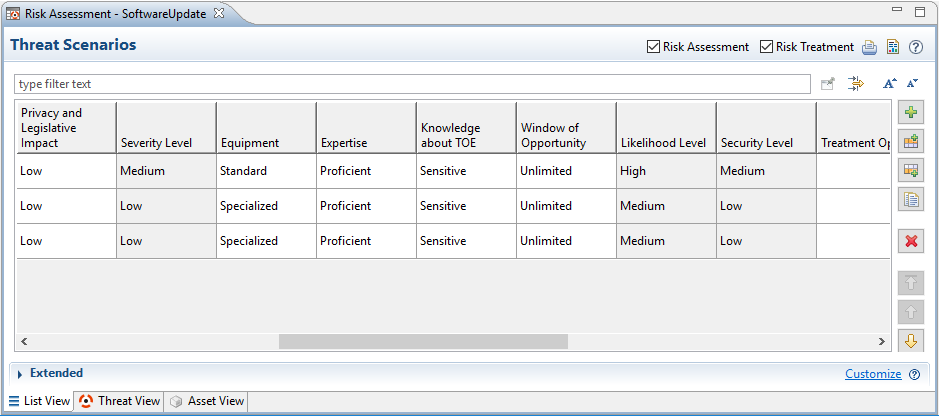 |
| Attack Trees | Attack Trees can be used to model how an asset, or target, might be attacked. A graphical attack tree editor was added in this release, combining known attacks and logical gates to complex attack scenarios leading to potential threats. Attack Trees can be used to detail attack paths and scenarios for threats and to estimate likelihood levels for threats based on attack knowledge, but also to observe the most effective way to mitigate a threat. 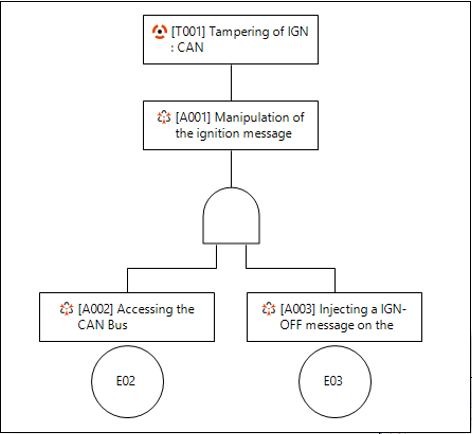 |


